
Fighting Ransomware: Part Two – ONTAP Native (aka Free) Tools for Detecting Ransomware

Matt Trudewind
 Wreaking havoc across the globe, ransomware is not expected to slow down as a threat anytime soon. Cybersecurity Ventures predicts that by 2021, a business will fall victim to a ransomware attack every 11 seconds. This is why many organizations are focusing on quick recovery, which they most certainly should.
Wreaking havoc across the globe, ransomware is not expected to slow down as a threat anytime soon. Cybersecurity Ventures predicts that by 2021, a business will fall victim to a ransomware attack every 11 seconds. This is why many organizations are focusing on quick recovery, which they most certainly should.
What if you could detect when a ransomware event starts to occur and then prevent it from spreading? It might sound like science fiction, but with NetApp® ONTAP® data management software, you have that capability built in. That means if you are running ONTAP, you can detect and prevent the spread of ransomware at no additional cost.
This blog post is the second in a six-part series that discusses how you can detect and prevent ransomware by using native NetApp® ONTAP® features, recover quickly from an attack, and avoid paying the ransom. It’s best to read them in chronological order:
- The first entry covered the objectives of cybercriminals and the largest portion of the cost of a ransomware attack, which is not the ransom.
- The second entry is focused on ONTAP native tools that you can use for early detection of a ransomware outbreak.
- The third entry took a deep dive into NetApp FPolicy® native mode, which helps prevent most older types of ransomware that are still prevalent today.
- The fourth entry focused on how to prevent the most modern variants of ransomware, including “zero-day” exploits, by using FPolicy external mode.
- The fifth entry highlighted the three key steps to successfully recover from a ransomware attack.
- The sixth entry focused on ONTAP Snapshot technology and how it provides very rapid restores (terabytes in seconds, not hours), protects your backups from ransomware encryption, and prevents deletion of valuable backup data.
What does ransomware actually do?
To understand how ONTAP native tools can help, it’s important to understand how a ransomware attack actually works. After a hacker infects a client machine with malware, ransomware encrypts the contents of files so that they are inaccessible without the encryption key. The encryption happens both on the infected client system and on network file shares. When the encryption process has finished and the user is locked out from accessing the files, the hacker demands a ransom payment to recover the files.
What does ransomware encryption look like from an ONTAP perspective?
To a user, it simply appears that the files can no longer be accessed, and there are typically lots of pop-ups demanding payment to access the files. However, it’s important to understand what is actually happening on the files stored on the ONTAP system. ONTAP administrators can then more easily spot typical ransomware behavior versus normal user file creation and modification.Although ONTAP software does not get infected with the ransomware, ONTAP storage virtual machines (SVMs) can contain encrypted user files that were placed there by the ransomware that is running on the client machine. The client machines have access to these network files either by SMB/CIFS shares or mounted NFS exports. As the files are encrypted, this activity effectively looks like new writes to the ONTAP file system. The original pre-encrypted data would still exist in the ONTAP file system in the form of a NetApp Snapshot™ copy. Only the pointers in the active file system are updated to reference the encrypted files. In the following example, blocks A, B, and C represent the original unencrypted files in the NetApp WAFL® file system, and blocks B1 and C1 represent the encrypted file changes. The active file system pointers have been updated to reference only blocks A, B1, and C1, but the original blocks B and C would still exist in the Snapshot copy (Snapshot copy 1).
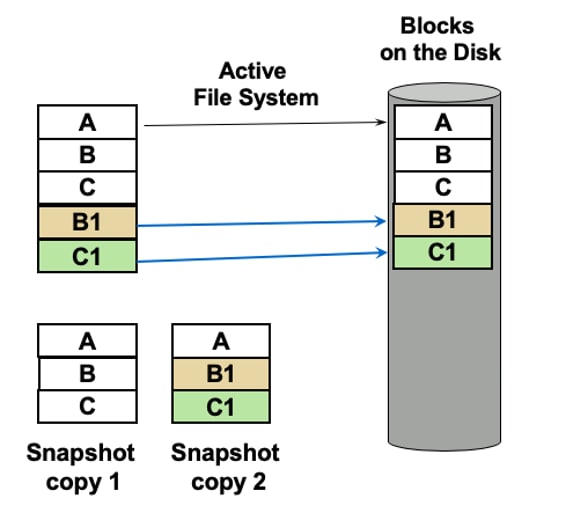 Snapshot copy 2 would now contain the encrypted files, which are referenced by blocks B1 and C1. This Snapshot copy would have a much larger size than Snapshot copy 1 because of the new writes for the ransomware encryption. You can see this in ONTAP System Manager by viewing the size and percent change for Snapshot copies.
Snapshot copy 2 would now contain the encrypted files, which are referenced by blocks B1 and C1. This Snapshot copy would have a much larger size than Snapshot copy 1 because of the new writes for the ransomware encryption. You can see this in ONTAP System Manager by viewing the size and percent change for Snapshot copies.
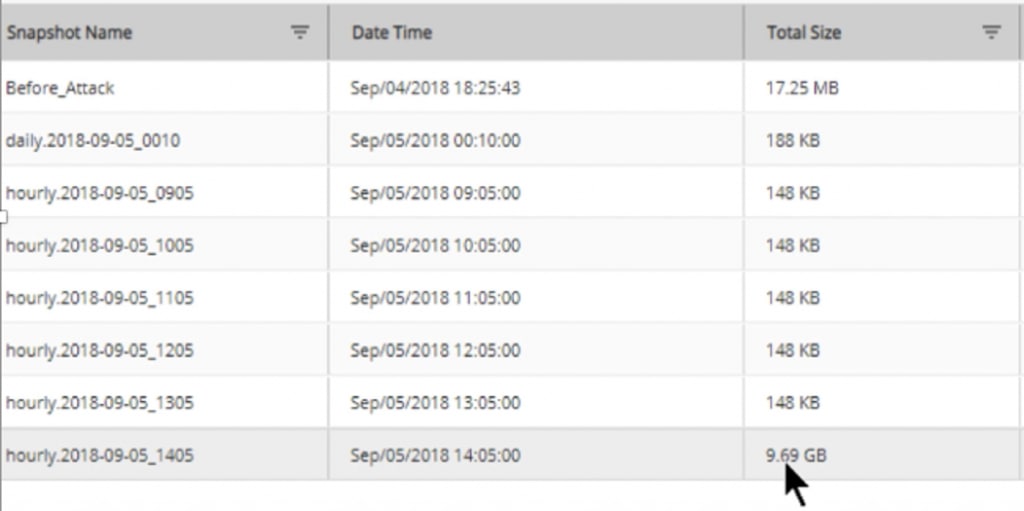 In this example, the most recent Snapshot copy has a total size of 9.69GB. Considering that the rest of the Snapshot copies are significantly smaller, this size is a good indication that you might have a ransomware attack occurring. It doesn’t always indicate an attack; there could be a legitimate reason why lots of data change has occurred. For example, perhaps someone has restored and overwritten a large amount of file data from a third-party backup device.
In this example, the most recent Snapshot copy has a total size of 9.69GB. Considering that the rest of the Snapshot copies are significantly smaller, this size is a good indication that you might have a ransomware attack occurring. It doesn’t always indicate an attack; there could be a legitimate reason why lots of data change has occurred. For example, perhaps someone has restored and overwritten a large amount of file data from a third-party backup device.
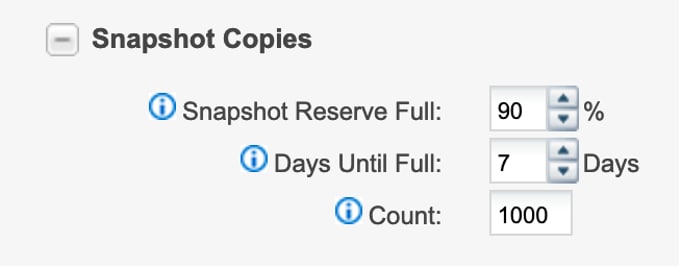
The ONTAP data management environment includes NetApp Active IQ® Unified Manager at no additional charge. This utility can also be used to alert you when the Snapshot reserve used percentage reaches a certain threshold (90% by default) or when a volume’s growth rate is abnormal (greater than 1% by default). Both alert conditions could indicate that a ransomware infection is in progress. After you’ve setup Unified Manager, you’re set to use this built-in alerting. Here is an example of these volume health thresholds and their default settings.
 For more information about this feature, see the Active IQ Unified Manager 9.7 Workflow Guide for Managing Cluster Health.
For more information about this feature, see the Active IQ Unified Manager 9.7 Workflow Guide for Managing Cluster Health.
Using storage efficiency measurements to detect ransomware attacks
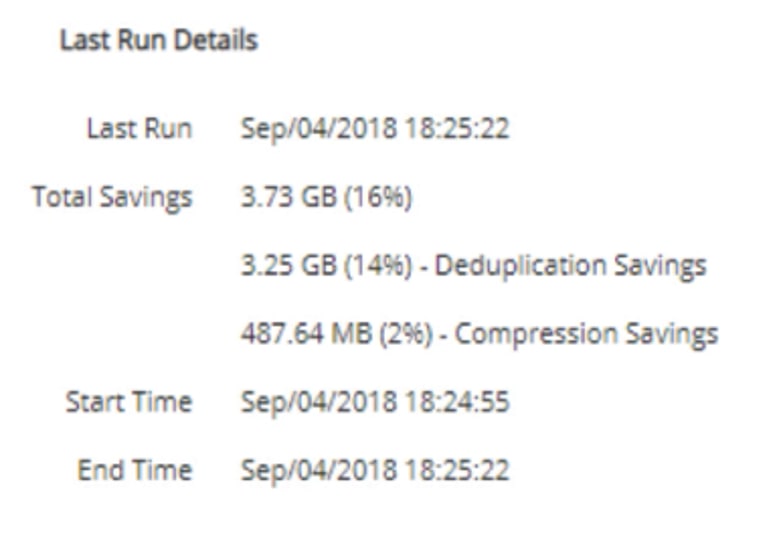
A large change in Snapshot size is not the only way to detect a potential ransomware attack. A significant decrease in storage efficiency is also a good indication of a ransomware encrypted dataset. Storage efficiencies involve space-saving features such as deduplication and compression. Deduplication finds common blocks among files and stores duplicate blocks only one time, eliminating redundancy and saving a large amount of storage space. When these blocks are encrypted at the client, ONTAP is not able to recognize similar blocks between files, because it cannot read the encrypted blocks. Likewise, encryption can also affect the efficiency of compressing data. Compression looks for similar patterns in data, and those patterns cannot always be found when the data is encrypted. Encrypted data appears to be randomized, and there is very little discernable pattern for the compression algorithm to recognize. As a result, both deduplication and compression gain very little storage efficiency when the data is encrypted by the host. The following example shows storage efficiency before and after a ransomware attack.Before an attack
 After an attack
After an attack
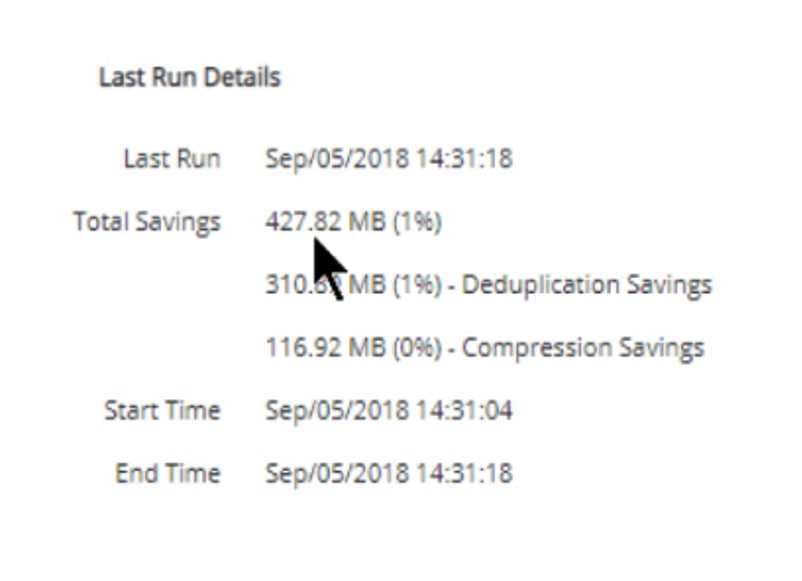 Deduplication percentage drops from 16% to 1%, and compression drops from 2% to 0. These changes can solidly indicate that a ransomware attack might be happening.
Deduplication percentage drops from 16% to 1%, and compression drops from 2% to 0. These changes can solidly indicate that a ransomware attack might be happening.
I’ve detected ransomware, but how do I stop or prevent it?
Using ONTAP and Unified Manager to monitor Snapshot rate of change and storage efficiency loss is an effective, no-cost way to detect ransomware. But what can you do to stop the ransomware in its tracks and prevent it from spreading? A great starting place is to note which volumes have an increase in Snapshot usage or a decrease in storage efficiencies. You can also determine which NFS or SMB file shares might be affected, because they will exist on the same volumes. But, as mentioned earlier, ransomware is run from the client machine, so it’s important to determine which clients are infected and what ransomware variant they might be infected with. To make this determination, you can use third-party tools such as anti-malware and antivirus scanners. In addition to third-party tools, you can use homegrown scripts to determine file modification dates.All of these items can lead you to the infected clients, so you can disconnect them from the network and prevent further spreading. However, this process can take time. That’s why the next blog in this series will focus on how you can quickly prevent and stop ransomware from spreading in an ONTAP environment by using the native ONTAP FPolicy feature. If you would like to get a jumpstart or learn more about the NetApp approach to ransomware, check out our technical report TR-4572: The NetApp Solution for Ransomware.
Matt Trudewind
Matt is a Security Evangelist at NetApp with a focus on ransomware prevention, cyber resiliency, and data-centric portfolio security. With 25 years of IT experience, he specializes in Zero Trust, Data Governance, Encryption, Security Tools, and Best Practices. Matt has held various roles at NetApp, including Product Manager and Technical Marketing Engineer for ONTAP Security. He also has extensive expertise in networking, SMB/CIFS, and Microsoft technologies. Matt's passion lies in driving the latest security features and capabilities to ensure customer success.