Fighting Ransomware: Part One – The History and Cost

Matt Trudewind

Although the situation may seem dire, it doesn’t have to be. NetApp® solutions help organizations recover quickly from ransomware with minimal impact, and they can also prevent ransomware from spreading in the first place.
This is the first blog in a series that covers how NetApp, and especially our flagship ONTAP® data management software, can help you to:
- Detect ransomware
- Prevent the spread of ransomware
- Recover quickly
- Avoid paying the ransom
- Stop day zero ransomware attacks
- Develop an overall ecosystem data protection strategy for ransomware
Before we dive into those topics, though, it’s important to understand what ransomware is as well as the real costs associated with a ransomware attack.
Ransomware: What is it?
The goal of an attacker employing ransomware is simply to make money as cheaply as possible. Over the years, the strategies used by attackers have evolved. In the past, attackers typically used a distributed denial of service (DDoS) attack, in which a corporation’s website that customers use to purchase items is made inaccessible. The DDoS would remain in place until a ransom was paid. Another method often used in the past is known as a data breach. With this strategy, the attacker gains access to a company’s IT systems, moving sensitive data to an unknown location outside of the company, and then threatens to publicly release that data unless a ransom is paid. However, both of these methods could prove too costly or time consuming for the attacker.
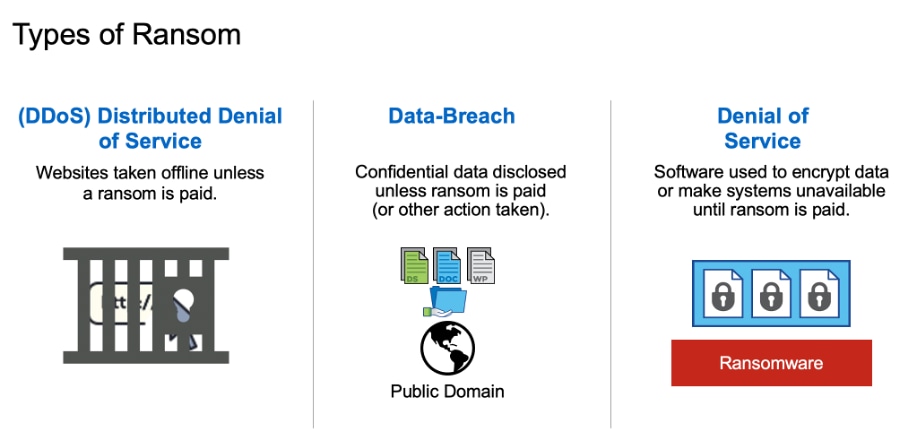
The modern version of ransomware, the one that most people are familiar with, is called denial of service. In this ransomware strategy, an attacker gets you to inadvertently download an encryption program (malware). Once installed, that malware encrypts all the local client files and also every single file that it can on NFS or SMB shares on the corporate network. Once the files are encrypted, the original files are deleted, and there is no longer any way for you to access the data in the files. You can still see the files, because they are still on your network. but you can’t access them, because the attacker has encrypted them.
In contrast to the earlier methods, denial of service has very low overhead for the attacker because they don’t have to summon an army of bots to take the corporate website offline, and they don’t need to copy your data out to another location. The attacker demands that you pay a ransom to obtain the decryption key so you can regain access to your data. The size of the ransom is typically large enough for the attacker to realize a sizeable chunk of money from the attack but not so large that it’s completely unrealistic for the organization to pay. The following figure shows a high-level overview of this process.
Ransomware: The real cost
You may be thinking that the ransom payment itself is the largest monetary impact on the business. However, although the payment is not insignificant (the average cost is believed to be as much as $84,116 per incident), it pales in comparison to the real cost of suffering a ransomware incident: downtime.
When an organization cannot access data that is critical to its business, productivity is severely impacted. According to a January 2020 analysis from Coveware, the average downtime from ransomware is more than 16 days, and “Downtime costs are typically 5-10x the actual ransom amount.” The impact and resulting cost of the downtime can vary from organization to organization, depending on the type of business. Organizations that rely heavily on IT availability (such as e-commerce, equities trading, and health care) are looking at the 10x cost factor. This means that the organization may be facing as much as $841,160 for the actual downtime suffered. Keep in mind that this amount is per incident; obviously, multiple incidents can increase the costs.
Keep in mind that these figures are averages, and these costs are expected to continue to rise as businesses become more reliant on IoT devices, which are also susceptible to ransomware attacks. For example, in 2019 a city government was crippled by ransomware for over a month, with an estimated loss of $18 million.
However, even though the situation appears dire, with the right solution there is a way to fight back against ransomware
Ransomware: What’s the solution?
Organizations can detect ransomware and prevent it from spreading with a User Behavioral Analytics (UBA) solution from NetApp, FPolicy® file screening, which we’ll cover in a future blog. Even when facing the worst-case scenario, recovery from a ransomware attack can be accomplished very quickly with NetApp ONTAP technologies. Plus, you can eliminate the costliest factor in a ransomware attack: downtime.
Check out the other blogs in this series (it’s best to read them in chronological order).
- The second entry focused on ONTAP native tools that you can use for early detection of a ransomware outbreak.
- The third entry took a deep dive into NetApp FPolicy® native mode, which helps prevent most older types of ransomware that are still prevalent today.
- The fourth entry focused on how to prevent the most modern variants of ransomware, including “zero-day” exploits, by using FPolicy external mode.
- The fifth entry highlighted the three key steps to successfully recover from a ransomware attack.
- The sixth entry focused on ONTAP Snapshot technology and how it provides very rapid restores (terabytes in seconds, not hours), protects your backups from ransomware encryption, and prevents deletion of valuable backup data.
To learn more about the NetApp solution for ransomware, check out these additional resources:
.png?width=117&format=pjpg&disable=upscale)